On the rather tight-lipped matter of privacy, there was more than a little fear-mongering going on in President Obama’s January 20 State of the Union address.
On the rather tight-lipped matter of privacy, there was more than a little fear-mongering going on in President Obama’s January 20 State of the Union address. Warning against legislative inertia that threatened to, “leave our nation and economy vulnerable” complete with malevolent hackers invading the privacy “especially of our kids” the President was clearly not above resorting to rhetorical flourishes that, while not devoid of truth-content, tend also to mask the privacy trade-offs inherent in centralized information sharing between government and industry. In the words of Mark Jaycox, legislative analyst with the Electronic Frontier Foundation, data-sharing between the private and public sectors, “creates this perfect storm for the potential of your personal information to be shared”. Thus a more measured approach seems justified given the high stakes.
Then again, perhaps measured responses have gone the way of powdered wigs as an even bleaker assessment was presented by a Harvard research group days later at World Economic Forum in Davos, Switzerland. Privacy is dead or at least it will never be resuscitated in any manner resembling, “how we conventionally think of it”, to quote researcher Margo Seltzer.
Certainly measured responses on the issue of privacy have proven elusive on the public sector side. One longstanding narrative is that security and privacy share a continuum. The strength of one comes only at cost to the other. However, this security-privacy construct is a false one. Government officials are nonetheless particularly fond of tossing these loaded dice. Here’s President Obama from June 2013:
“I think it’s important to understand that you can’t have 100 percent security and then have 100 percent privacy…We’re going to have to make some choices as a society.”
Then, former NSA Security consultant Ed Giorgio in 2008:
“We have a saying in this business: ‘Privacy and security are a zero-sum game.’”
Absolutes are practical non-starters. This is no less the case in the privacy debate. Absolute security, theoretically possible, would require a ban on crossing the street. As for absolute privacy, solitary confinement has its champions. However that seems more punishment than aspiration. Ultimately, all continua are couched within that great overarching zero-sum called life, a 100% fatal enterprise in all cases. Suffice to say, we’re forever balancing extremes. Zero-sum formulations in the privacy arena make for particularly bad straw-men. When government trots them out, there’s often more than bumbling bureaucratese at work. For reasons we’ll show, the security-privacy dichotomy is falsely constructed by design.
Indeed the real trade-off is not between security and liberty at all. Since at least the early aftermath of 9/11, Bruce Schneier of Harvard’s Berkman Center for Internet & Society has been monitoring and deconstructing the semantic mischief in his weekly ‘Schneier on Security’ column. Here he is in May 2006: “Too many wrongly characterize the debate as ‘security versus privacy.’ The real choice is liberty versus control.” Now there’s a trade-off with some cognitive heft.
Immediately one sees why government might be hedging its intent with obfuscating continua. After all, ‘control’ conjures unpleasant images of incarceration, restraint, repression, loss of autonomy. Better not use it even when one means it. No government is going to pre-announce a decided turn toward despotism. Instead it will couch the turn in security terms. Trundling out the terror bogeyman greases the despotic skids.
There’s an argument Government is unwittingly conflating its security with ours. That is, in a bid to secure its power, Government might have convinced itself society-at-large is best served by curtailing our liberties. However, motive shouldn’t matter when the end result is the same. We’ve all heard about the road to hell where good intentions are well-beaten pavestones. Should the historic footnote end up reading, privacy perished in America through a series of well-intentioned, bureaucratic missteps, our locked-down condition will be no less restrictive. (For an interesting chronicle of the advancing cyber-security state, Nate Anderson’s 2014 book ‘The Internet Police: How Crime Went Online, and the Cops Followed’ is worth a read. This author reviews it here.)
Have Americans gained any security upticks, even by accident, from the over-decade-long, multi-billion dollar prosecution of a false dichotomy? Schneier intends no sarcasm when he suggests only three modest benefits: “reinforcing the cockpit doors, passengers realizing they have to fight back and—possibly—sky marshals.” The rest, he calls ‘security theatre’. Incidentally, none of the three security enhancements invaded personal privacy.
Patrician equivocations from our Government have a historic precedent. In a 1971 speech before the National Press Club, CIA Director Richard Helms launched a broadside both at our nation’s divided system of government and Congressional oversight with an oddly plaintive justification for extra-constitutional espionage. Repeatedly asked about the CIA’s covert forays in foreign lands, he declared: “You’ve just got to trust us. We are honorable men”.
Blind trust is a nonstarter. On the subject of good guys and bad guys, the Constitution is cynically agnostic by design. A dark vision perhaps, but absolute power has a perennial tendency of stripping men and women of their honorable dispositions.
 In the final analysis, no one can be a friend to privacy except the People themselves. But only if they feel their privacy warrants protection. Every day on Facebook, millions of people share with the world what they had for breakfast. Privacy must be re-esteemed at the grassroots, one breakfast table at a time.
In the final analysis, no one can be a friend to privacy except the People themselves. But only if they feel their privacy warrants protection. Every day on Facebook, millions of people share with the world what they had for breakfast. Privacy must be re-esteemed at the grassroots, one breakfast table at a time.
Jim Harper, Director of Information Policy Studies at The Cato Institute, offers a very workable definition for privacy [my italics]: “…the subjective condition people enjoy when they have power to control information about themselves and when they exercise that power consistent with their interests and values.”
Harper echoes Schneier in recognizing control as an essential aspect of privacy. Not being able to do things is a palpable deprivation everyone can feel and understand. Through the exercising of self-control, an individual’s privacy maintains its inherent sanctity. And yet, Government invariably begs to differ. Here’s Donald Kerr, principal deputy director of National Intelligence, (from You Get Privacy When Your Definition Matches Ours’ Ars Technica, by Ken Fisher, Nov 11 2007):
“Americans need to shift their definition of privacy to center instead on the proper maintenance and protection of personal data by government and business entities…privacy, I would offer, is a system of laws, rules, and customs with an infrastructure of Inspectors General, oversight committees, and privacy boards on which our intelligence community commitment is based and measured.”
First of all, the paternalistic tone is off-putting and instructive in and of itself. Shouldn’t proposed shifts in privacy be a grassroots referendum and not a top-down directive from the spy community to the open society that ostensibly employs it? Kerr seems to be suggesting nothing less than that Harper’s ‘subjective self’ report immediately to the public square for government inspection. This creates a conundrum since a human being’s private realm, ordered to present itself for review before Kerr’s battery of boards and ‘oversight’ committees, relinquishes its private status solely by virtue of showing up. This is a Rubicon dilemma. Once de-privatized, privacy content can never be re-privatized. The NSA is clearly pressing a third category: collected but not actively reviewed. Call it restored virginity. Who’s buying that on their wedding night?
Clearly, mass and indiscriminate surveillance is, for Kerr, a settled debate. (That’s because the NSA had already settled it unilaterally and to its own satisfaction. The 2007 quote would betray its cagey circumlocution in the subsequent Snowden revelations.) Our data was already in their hands. Privacy has thus already been coopted by a great, indiscriminate and a priori NSA vacuum cleaner. The debate for Kerr thus begins after surveillance has occurred i.e. at a bumped-forward time-zero. To use an operable government euphemism, Kerr was being ‘less than candid’ with us.
Or as Ken Fisher puts it, Kerr artfully skips a page right on over to, “…how such data is safeguarded” once it has been collected. Of course had it never been collected in the first place, all talk of safeguarding and maintaining it would be unnecessary. That public debate never occurred. Government is indeed reprising Helms’ shadowy third way. Trust us. We are honorable men.
So, we’re up against two very different definitions of privacy in America. One is a priori, inalienable and subjectively sacrosanct to the individual. The other defines a privacy that can be ‘won back’ from a surveillance apparatus that invades it at the outset as a matter of course. This is more than a little unsettling as Government seems to be making of a zero sum a less-than-virtuous closed circle: ‘Because we are everywhere, we are nowhere’. Excusing demagoguery on the grounds that it’s managed a cool approximation of godlike omnipresence is unchecked, unbalanced and unconstitutional in the extreme. In true Orwellian fashion, we’re left with a definition of privacy that’s the antithesis of privacy.
Another conceptual demarcation crucial to the privacy discussion and yet prone to its own form of vagueness is privacy versus liberty. Our Constitution may betray its age most vividly here as, in the pre-electronic age, notions of ubiquitous surveillance were technical non-starters. Can we say private lives in 18th century ‘unwired’ America were uncontested givens? In ‘The Two Western Cultures of Privacy: Dignity versus Liberty’, James Whitman lays the privacy crisis at the feet of the modern era: “It is a commonplace, moreover, that our privacy is peculiarly menaced by the evolution of modem society, with its burgeoning technologies of surveillance and inquiry.” Thus while the Bill of Rights explicitly enumerates various rights and liberties, the closest we get to a ‘right to privacy’ resides, albeit implicitly, in the ‘unreasonable searches and seizures’ clause of the Fourth Amendment. Privacy rights are also implicitly addresses elsewhere in the Constitution and in subsequent court cases such as the landmark Roe vs. Wade.
Whitman goes on to suggest the varying American and European notions of privacy spring from two different value systems, each finding its essential origins in the 18th century: “On the one hand, a European interest in personal dignity, threatened primarily by the mass media; on the other hand, an American interest in liberty, threatened primarily by the government.” Furthermore, neither of these worldviews is necessarily exclusive as, “the contrast…is relative and not absolute. Moreover, there is no logical inconsistency in pursuing both forms of privacy protection.” For our purposes here, we’ll stick with the American version of privacy and liberty where, as Whitman suggests, liberty (in direct contraposition to government control) enjoys a much more storied tradition.
An argument could be made that the government is seizing the initiative to cast privacy in a decidedly authoritarian frame because no explicit privacy right is asserted by the Constitution. This ‘government goes first’ approach upsets the notion that un-enumerated rights belong to the People while only expressly codified powers belong to the government. Yet, in this anxious and bewildering age where terror has proven itself such a potent, if controversial, organizing principle, the authoritarian model enjoys remarkably uncontested traction.
In the healthcare field, recent laws such as HIPAA and HITECH define Personally Identifiable Information (PII) for specific privacy protections. Indeed the evolution of privacy law in the U.S. tends to follow and augment preexisting industry-specific laws. Nonetheless, as Dr. Tim Godlove points out in his upcoming book ‘Guide to Healthcare Information Protection and Privacy’, the judicious handling of PII creates a work environment riven with, “perpetual contradictions making security and privacy policies difficult to enforce.”
There is no doubt privacy and liberty are conceptually adjacent, if not in some sense zero-sum. For example, I cannot exercise my liberty to the point of infringing upon your privacy as would happen if I was to peer through your living room window. We have here a legitimate continuum worthy of negotiated accommodation.
Beyond the very real cultural differences that inform notions of privacy the world over (and which will increasingly assert themselves in business interactions between the US and EU), the tensions between government claims and personal sensibilities here in the States are where the real fireworks are most likely to occur.
While constitutional delineators of privacy may be lacking, the field of psychology offers much on the human need for privacy. In his Wired article ‘What Our Top Spy Doesn’t Get: Security and Privacy Aren’t Opposites’, Bruce Schneier (who’s frankly reached ‘guru’ status in the privacy space though he bristles at the term) touches briefly upon psychologist Abraham Maslow’s famous work: “Even if you don’t subscribe to Maslow’s hierarchy of needs, it’s obvious that security is more important [than privacy]. Security is vital to survival, not just of people but of every living thing.”
Schneier is really onto something that warrants further exploration. Indeed Maslow’s famous hierarchy of needs offers yet another way into the security-privacy false dichotomy. Maslow’s hierarchy can be summed up thusly (from Goble, F., The Third Force: The Psychology of Abraham Maslow [Maurice Bassett Publishing, 1970], p. 62):
“The most fundamental and basic four layers of the pyramid contain what Maslow called ‘deficiency needs‘ or ‘d-needs‘: esteem, friendship and love, security, and physical needs. If these ‘deficiency needs‘ are not met – with the exception of the most fundamental (physiological) need – there may not be a physical indication, but the individual will feel anxious and tense. Maslow’s theory suggests that the most basic level of needs must be met before the individual will strongly desire (or focus motivation upon) the secondary or higher level needs.”
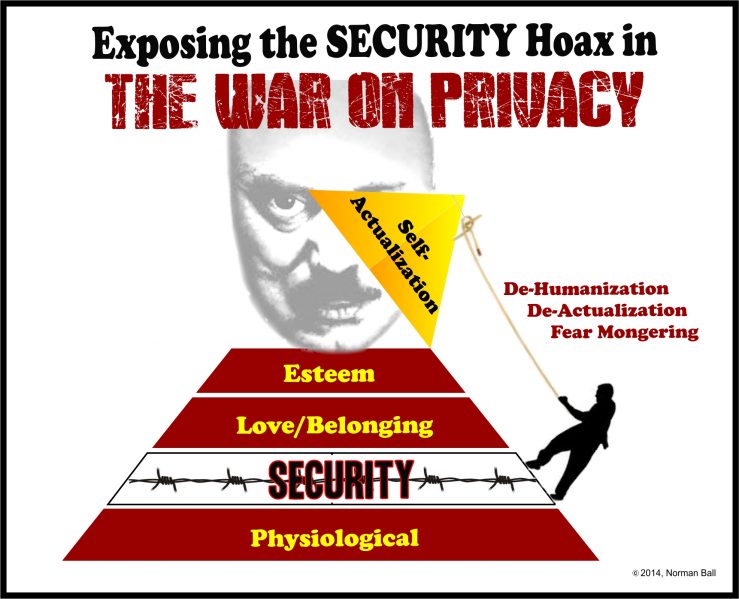
Maslow based his research on exemplary individuals. He believed psychology’s perennial attention to ‘crippled and stunted’ individuals yielded a ‘cripple psychology’. [This author notes that the term ‘cripple’ has become offensive to many in the decades since Maslow’s use of it; alternate descriptions will be used hereon.] That may be so. But as we will explore shortly, power has an unfortunate habit of attracting the psychologically impaired. Thus pathology and dysfunction among the powerful may be the rule and not the exception. The truth is there are fundamentally insecure people for whom security/safety needs can never be adequately met. When such individuals acquire power over others these deficiencies have a multiplicatively adverse effect. A manipulative few can also wield fear-mongering to heighten the perceived deficiency in security measures beyond all rational considerations. (Tellingly, Maslow happens to call all needs below self-actualization ‘deficiency needs’.) Thus the security/safety need fixation can serve as a cul de sac to which many people (if not entire societies) are forever relegated.
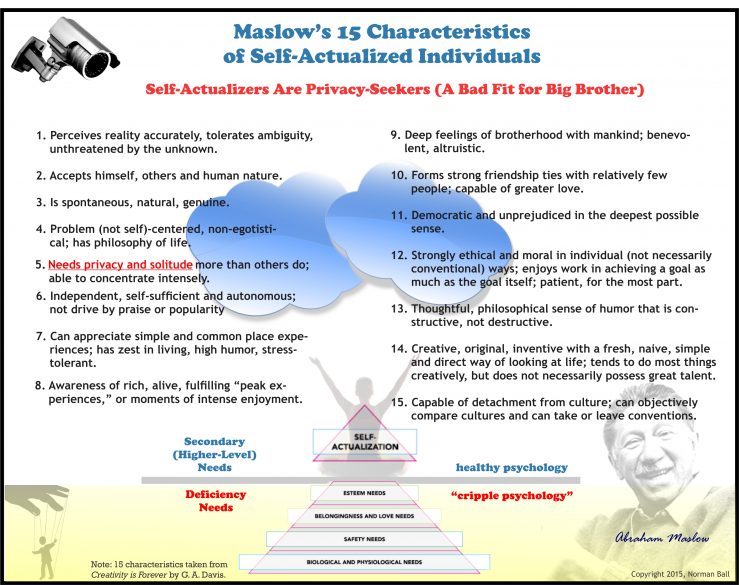
Then there is that copacetic vanguard in our midst, the self-actualizers. Maslow cites fifteen characteristics of the self-actualizing individual. It’s not hard to imagine a security-fixated society being hostile to most of these ‘break-out’ characteristics. They are expansive and libertarian in tone, anti-statist and stridently individualistic.
One of these characteristics is of particular interest to the current discussion. Self-actualizers (no more than 2% of any population) require, “privacy and solitude more than others do”. Once again—this time courtesy of Maslow—we find the privacy-security equivalency in an apples-and-oranges quandary. Security is a deficiency need. The desire for privacy is an ascendant characteristic. Might the public policy fixation on security—as though it were an ascendant societal aim—covertly harbor the desire to unseat our rare and precious self-actualizers?
Absent proper checks and balances, we can see how the state security apparatus could decapitate the self-actualizing process. A retrograde, fear-based project of de-actualization works to dehumanize a society. Take an individual’s longstanding walk around his neighborhood—for him or her, a crucial interlude of self-reflection suddenly discontinued for fear of an alleged neighborhood terror cell. This tiny retreat from personal self-actualization becomes a victory for the security apparatus. Imagine such prohibitions magnified a thousand times in a thousand different ways across an entire society?
Often, intelligence officials will offer, ‘if you only knew what we’d protected you from, you’d gladly welcome and appreciate our incursions into your private life’. Of course the very secrecy (state privacy?) that the government insists upon for itself precludes it from telling us exactly what we’ve been saved from. We are back to the honorable men conundrum, leaving us to prove negatives or blindly trust those who increasingly appear to be wielding near-absolute power over us.
If the security-at-all-costs dynamic succeeds in ‘protecting’ us by extinguishing the American way of life, what have we been protected for? In crucial and fundamental ways, We the People and the privacy that defines us have been sacrificed. The same river is never crossed twice. Is any security measure really ‘for us’ if it succeeds in making us unrecognizable to ourselves?