Pennymac Mortgage Investment Trust (NYSE: PMT) Stock Price Enters Oversold Territory With RSI At 29.1 And A 12.31% Dividend Yield
Jun 9, 2026
Pennymac Mortgage Investment Trust (NYSE: PMT) has attracted fresh attention from dividend-focused...
Read MoreApple (NASDAQ: AAPL) Unveils Siri AI Overhaul As Tim Cook Prepares To Exit
Jun 9, 2026
Apple (NASDAQ: AAPL) announced a sweeping update to its Siri digital assistant at its annual...
Read MoreHakeem Jeffries Says Affordability Will Be Top Priority If Democrats Retake House Majority
Jun 9, 2026
House Democratic Leader Hakeem Jeffries has signaled that economic relief for working Americans...
Read MoreLululemon (NASDAQ: LULU) Slashes Annual Forecast As Stock Price Hits Eight-Year Low
Jun 9, 2026
Lululemon Athletica (NASDAQ: LULU) shares tumbled more than 12% following its fiscal first-quarter...
Read MoreOracle (NYSE: ORCL) Drops Nearly 10% In Worst Session In Months As AI Fears Mount Ahead Of Earnings
Jun 9, 2026
Oracle Corporation (NYSE: ORCL) suffered a sharp decline of nearly 10% on Friday, marking its...
Read MoreNetflix (NASDAQ: NFLX) Stock Price Impactedas Board Transition Elevates Jay Hoag, Reed Hastings Exits Chairman Role
Jun 9, 2026
Netflix (NASDAQ: NFLX) has announced a significant governance transition, with co-founder Reed...
Read MoreCannabis Sector Struggles To Turn Early Excitement Into Lasting Profit
Jun 9, 2026
The cannabis industry, once celebrated as one of the most promising emerging sectors in global...
Read MoreBillionaire Daniel Loeb Backs Meta (NASDAQ: META) And Alphabet (NASDAQ: GOOGL) As AI Spending Race Intensifies
Jun 9, 2026
Hedge fund billionaire Daniel Loeb added significant positions in two of the world’s largest...
Read MoreFactorial Energy Goes Public Via SPAC Merger, Shares Surge 16% On Debut (NASDAQ: FAC)
Jun 9, 2026
Factorial Energy (NASDAQ: FAC), an advanced-technology battery company targeting the electric...
Read MoreAmazon Deal Sends Corning (NYSE: GLW) Surging As AI Data Center Demand Accelerates
Jun 9, 2026
Corning (NYSE: GLW), the glass and electronic component manufacturer, saw its shares jump 7.4% in...
Read MoreRTX (NYSE: RTX) Unit Raytheon Commits $100 Million To Rhode Island Expansion As Missile Defense Demand Surges
Jun 9, 2026
Raytheon, a business of RTX (NYSE: RTX), is investing $100 million to expand its Portsmouth, Rhode...
Read MoreBitMine Immersion Technologies (NASDAQ: BMNR) Closes In On 5% Of Ethereum Supply With 5.5M ETH Stack
Jun 9, 2026
BitMine Immersion Technologies (NASDAQ: BMNR) has accumulated approximately 5.5 million ETH,...
Read MoreWedbush Says Apple (NASDAQ: AAPL) WWDC Signals A Foundational AI Consumer Platform Shift With Siri AI Unveiling
Jun 9, 2026
Apple Inc (NASDAQ: AAPL) kicked off its annual Worldwide Developers Conference with what Wedbush...
Read MoreNebius Group (NASDAQ: NBIS) And SoundHound AI (NASDAQ: SOUN) Face Off As Top AI Investment Picks For 2026
Jun 9, 2026
Nebius Group N.V. (NASDAQ: NBIS) and SoundHound AI (NASDAQ: SOUN) represent two distinct...
Read MoreOcasio-Cortez Labels Trump’s Knicks Game Appearance A ‘Vibe Killer’ Over Watch Party Disruptions
Jun 9, 2026
New York Representative Alexandria Ocasio-Cortez has criticized President Donald Trump’s...
Read MoreApple (NASDAQ: AAPL) Stock Price Drops Nearly 2% After WWDC AI Siri And Apple Intelligence Reveal
Jun 9, 2026
Apple (NASDAQ: AAPL) closed Monday’s session at $301.54, falling 1.89% despite an earlier...
Read MoreDell (NYSE: DELL) Surges 54% And HP Enterprise (NYSE: HPE) Jumps 59% In A Month As AI-Server Orders Explode
Jun 9, 2026
Dell Technologies (NYSE: DELL) and Hewlett Packard Enterprise (NYSE: HPE) have staged remarkable...
Read MoreNeedham Reiterates Buy On Applied Digital (NASDAQ: APLD) With $66 Share Price Target
Jun 9, 2026
Applied Digital Corporation (NASDAQ: APLD) received a reiterated Buy rating and a $66 price target...
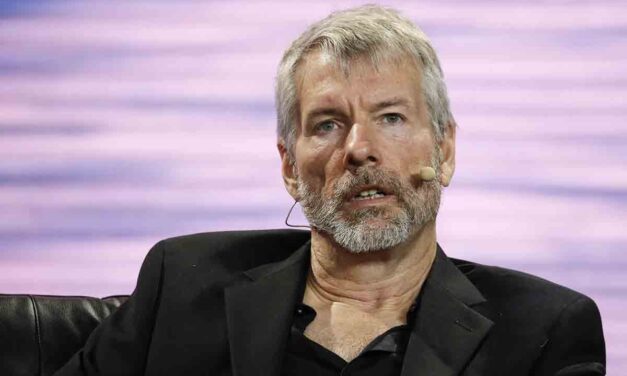
Read MoreStrategy (NASDAQ: MSTR) Stock Price Takes Hit After Saylor Abandons Bitcoin-Per-Share Focus
Jun 9, 2026
Strategy (NASDAQ: MSTR) reversed course last week, purchasing bitcoin under market conditions that...
Read MoreGameStop (NYSE: GME) CEO Ryan Cohen Pushes Forward On eBay (NASDAQ: EBAY) Acquisition Despite Board Rejection
Jun 9, 2026
GameStop (NYSE: GME) CEO Ryan Cohen is pressing ahead with his bid to acquire eBay (NASDAQ: EBAY),...
Read More